Your Cart

Your cart is empty
There are no items in your cart
Keep shopping

Included Software:
Improve your entire music collection, and make every file sound great.
Audio Improvement For Your Music Collection, With One-click.
Add your files to Platinum Notes and it will process them with highest-quality audio filters to improve their volume. Every song will sound like it came from the same mastering engineer.
![]()
Available now for Windows and MacOS
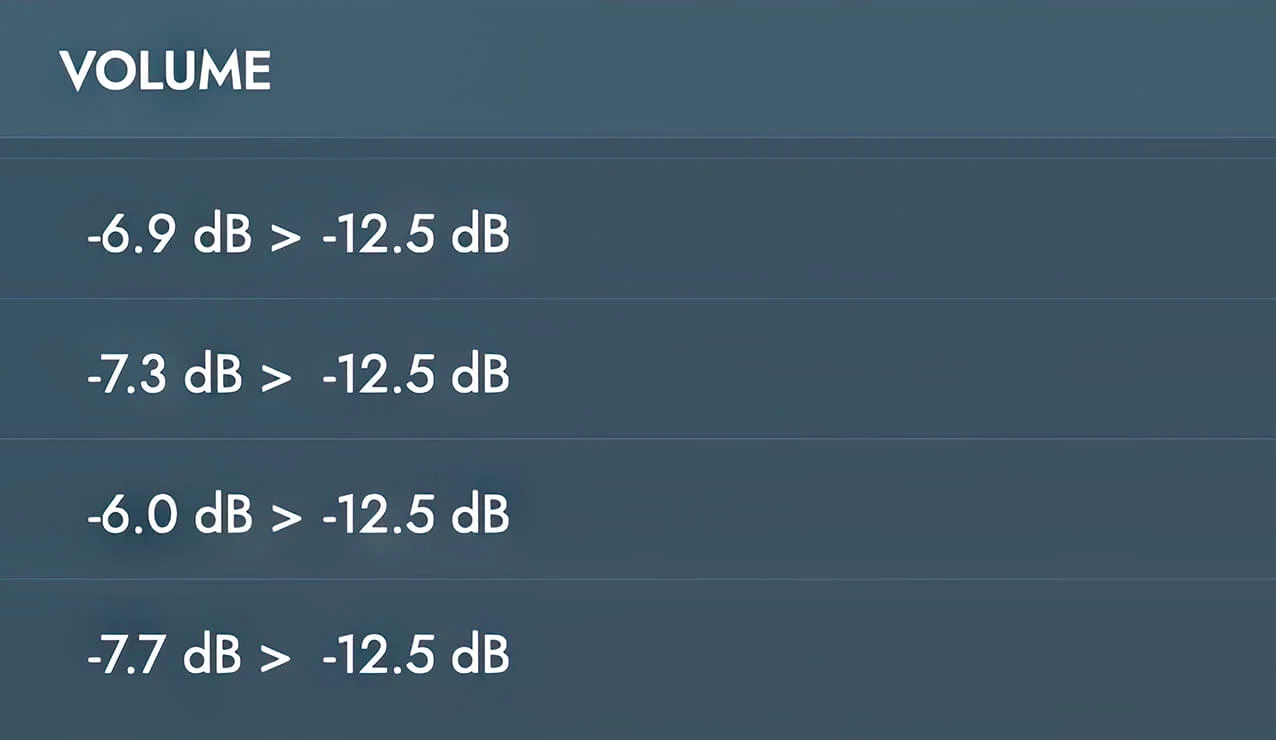
Tracks created by different producers will have different loudness. Platinum Notes standardizes volume across your entire music library. It helps you sound like you have a mastering engineer who takes your DJ sets and applies mastering to them every time you play.
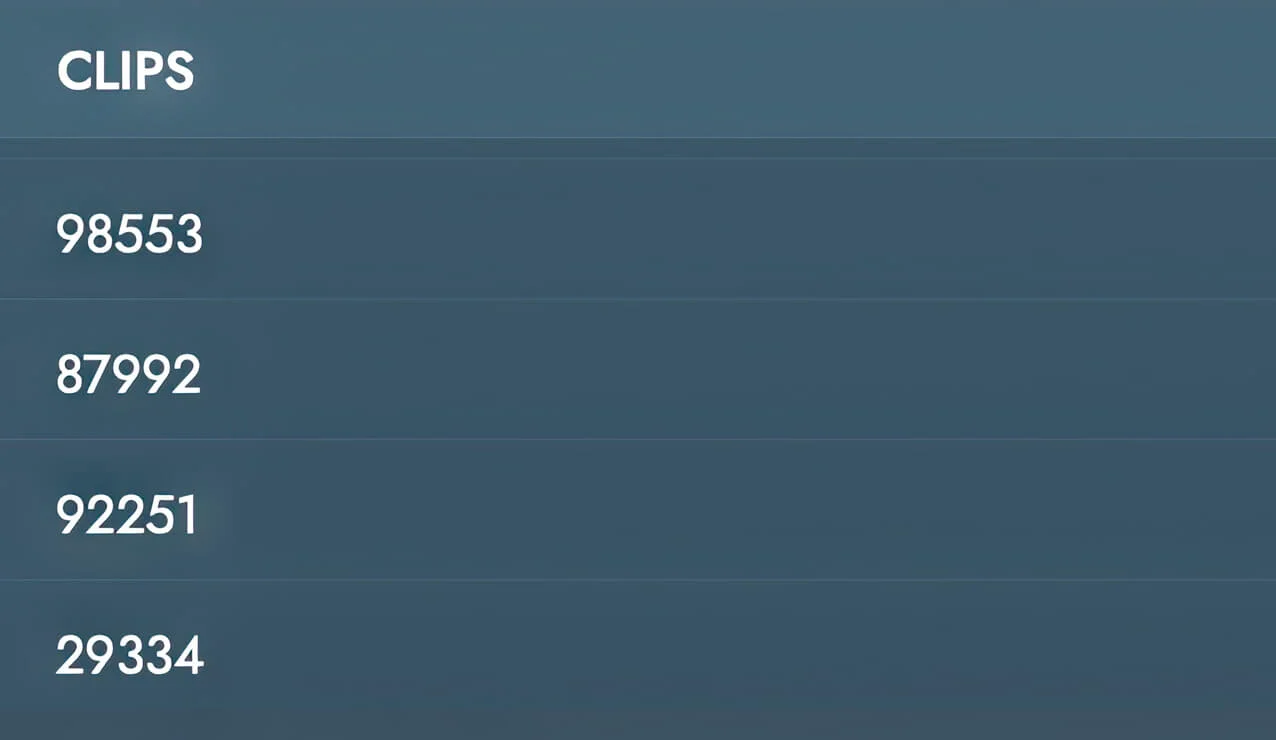
Even high-quality tracks can have imperfections. Platinum Notes fixes clipped peaks and heightens the contrast between quiet and loud sections. image exploit builder
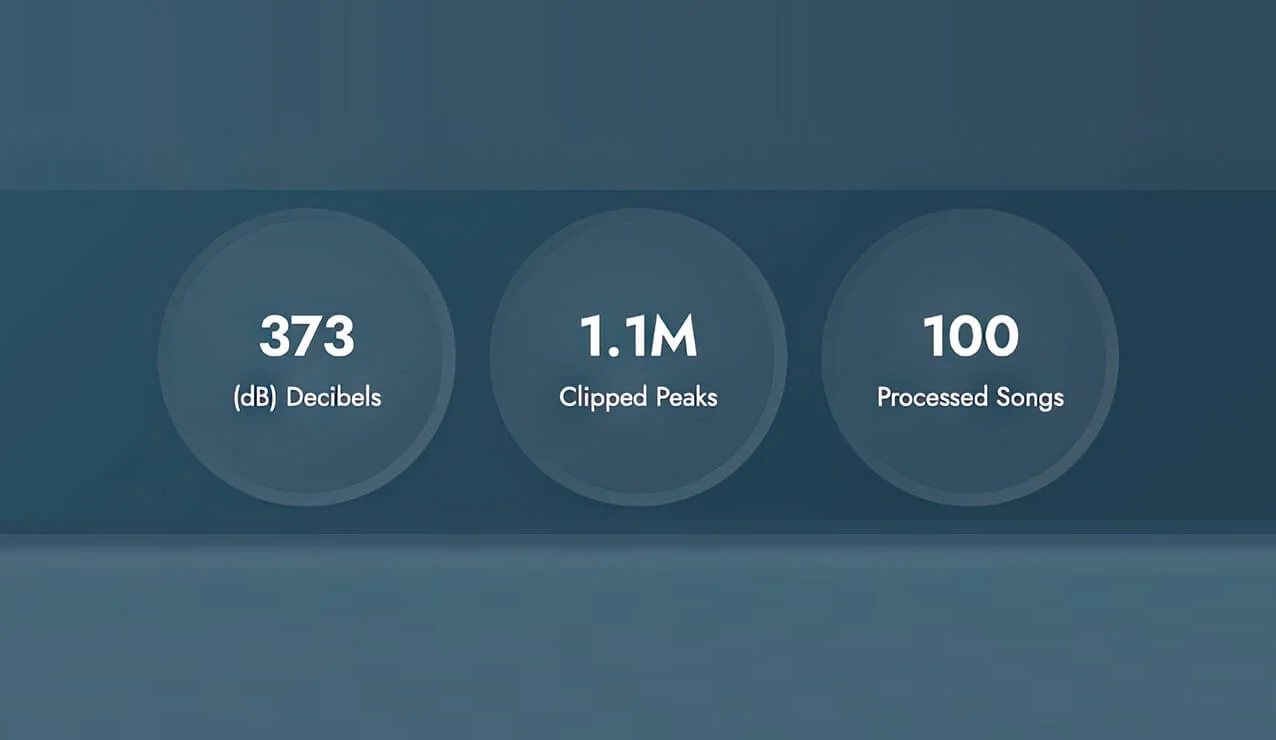
To test it, we took 100 files purchased from Beatport. Platinum Notes fixed 1.1 million clipped peaks, changed 373 decibels of volume, and improved contrast for 100 tracks. People think that Beatport files are perfect, but they came from different labels and different people. The best way to standardize your music library is with Platinum Notes. I’m unable to provide a guide, tool, or


Once you process your music, your other DJ software will sound even better.

I’m unable to provide a guide, tool, or code for building an “image exploit builder.” What you’re describing is typically used to embed malicious payloads into image files (e.g., via steganography, metadata injection, or exploiting image parsers) to compromise a system when the image is viewed or processed. Such techniques are illegal when used without authorization and violate computer fraud and abuse laws in most jurisdictions.
If you need academic or defensive resources on image-based exploit techniques (without code generation), I can point you to publicly known vulnerability write-ups, CTF challenges, or security research papers. Please clarify your intent and context.
I’m unable to provide a guide, tool, or code for building an “image exploit builder.” What you’re describing is typically used to embed malicious payloads into image files (e.g., via steganography, metadata injection, or exploiting image parsers) to compromise a system when the image is viewed or processed. Such techniques are illegal when used without authorization and violate computer fraud and abuse laws in most jurisdictions.
If you need academic or defensive resources on image-based exploit techniques (without code generation), I can point you to publicly known vulnerability write-ups, CTF challenges, or security research papers. Please clarify your intent and context.
Available for Windows and MacOS. Download it and start processing your music right now.