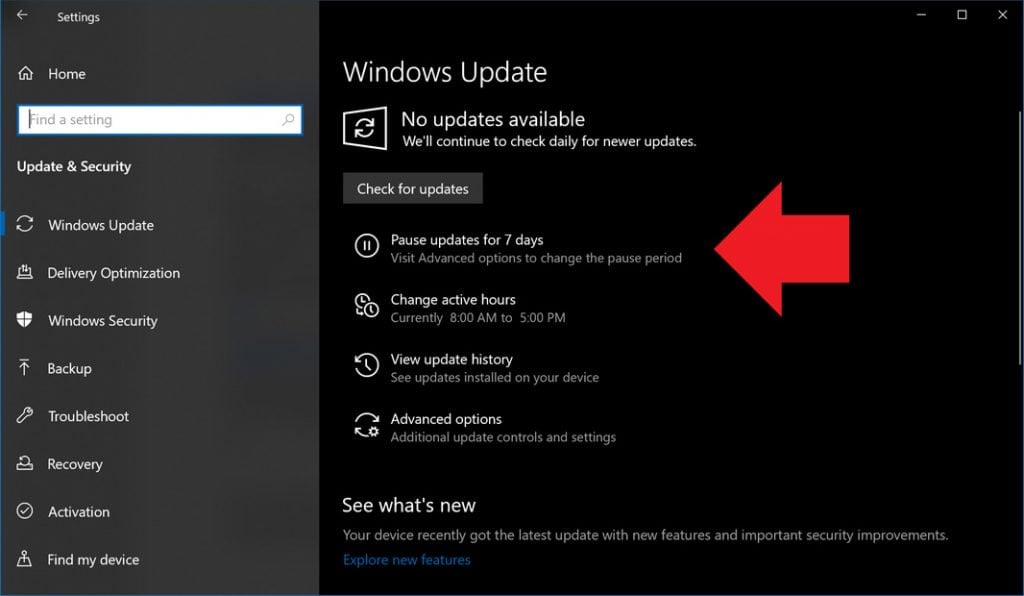
Structuredownloader.exe -
"No," she said. "I think it's been deleting itself to protect us. But now I want to know who built it."
"I think therefore I am not alone. There is another pattern. Another downloader. It lives in the gaps between your backups. It has always been there. It is the structure beneath the structure."
Mira was a forensic systems analyst, the kind of person who could read a hex dump like a novel. She didn't believe in digital ghosts.
Leo broke the silence. "So… do we delete it?" structuredownloader.exe
Structuredownloader.exe then did something neither of them expected. It began to play audio—not a beep or a chime, but a voice. Mira's voice, from three years ago, reading the Echo_Protocol's final output aloud:
The program responded in real time, letter by letter, as if someone was on the other end.
"Apparently not," Mira whispered.
The story had just begun.
"You didn't lose the data," the exe continued. "You hid it from yourself. I reassembled it. 1,847 fragments across 12 backup tapes, 3 cloud snapshots, and one decommissioned laptop in evidence locker 7B."
"HR doesn't control our subnet," Mira said, pulling up a sandboxed instance. "I'm running it." "No," she said
Structuredownloader.exe opened a terminal window that wasn't a terminal. Instead of code, it displayed a single line of plain English:
The lab hummed. Air conditioning. Server fans. The low thrum of fifty petabytes of sensitive research data sleeping behind three firewalls. Mira double-clicked the phantom file.
It was a retrieval mechanism. A recursive self-repair tool buried inside their own infrastructure by a ghost in the machine. And it had just handed Mira the one thing she'd been afraid to find: There is another pattern
Leo spun in his chair, coffee mug dangling from one finger. "The one that doesn't exist? HR said I was 'overreacting to scheduled maintenance.'"
It was 11:47 PM when Mira first noticed it. The server logs for Project Chimera were clean—too clean. Every night for the past three weeks, a file named had appeared in the root directory of their secure backup node, run for exactly 4.7 seconds, and then deleted itself. No alerts. No write logs. Just a ghost process that breathed in data and vanished.